Dodgy HSBC Authentication
Posted April 24, 2017; 2 min read
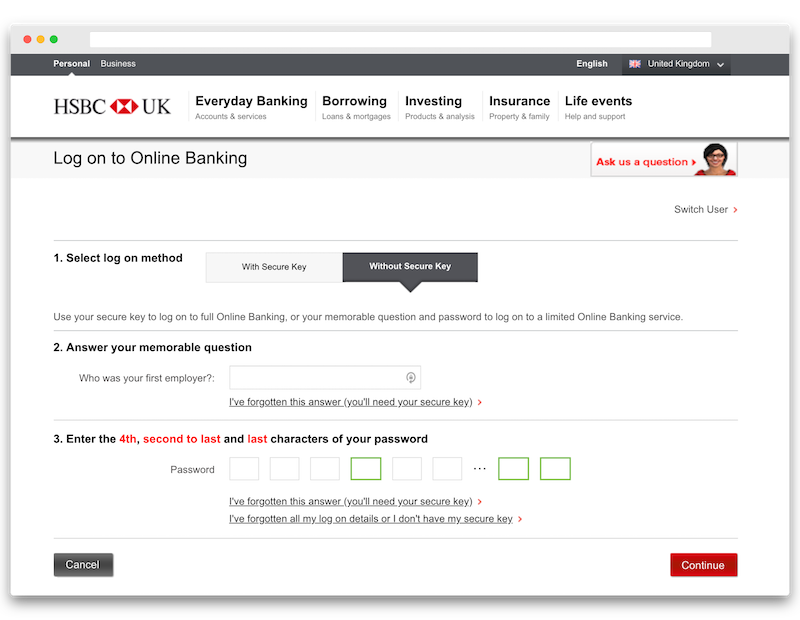
HSBC supports two forms of authentication.
The first involves logging in using your username and a One-time Passcode (OTP) generated by a physical or digital keypad, which provide similar security to using a Multi-factor Authentication (MFA) app like Google Authenticator or Duo. This provides the highest level of privilege to your bank account and lets you send money to other accounts that you haven’t previously interact with.
The second involves logging in using your username, the answer to a memorable question and certain characters of your password. The latter is done to protect against key loggers, which may be running on shared or compromised devices. This providers a lower level of privilege to your bank account, but still lets you view account numbers and transaction history.
Questionable practices
The second form of authentication described above does not follow best practices and has frustrated me (and others) since I opened my HSBC account. Some of the glaring issues with this approach are:
- Your password is not hashed and salted, which is the industry standard. If there is a security breach, your password could be leaked and decrypted, if necessary.
- You cannot easily use a password manager to enter your password characters. This results in users using weaker passwords.
- Memorable questions and answers are easy to guess and if leaked, you cannot change them without lying.
- Requiring a subset of characters reduces the strength of your password as attackers need only guess these characters instead of your entire password, once they have confirmed your memorable answer.
Protecting yourself
Firstly, don’t answer your secret questions correctly! Instead, have your password manager generate a random password and use this as the answer to your secret questions. The real answers to most security questions (e.g. Who was your first employer?) should be considered public knowledge.
Secondly, it is especially important not to reuse your HSBC password anywhere else. If HSBC experiences a password breach, your password might be recoverable as it is not hashed and attackers could access other accounts that use the same password.